
Member
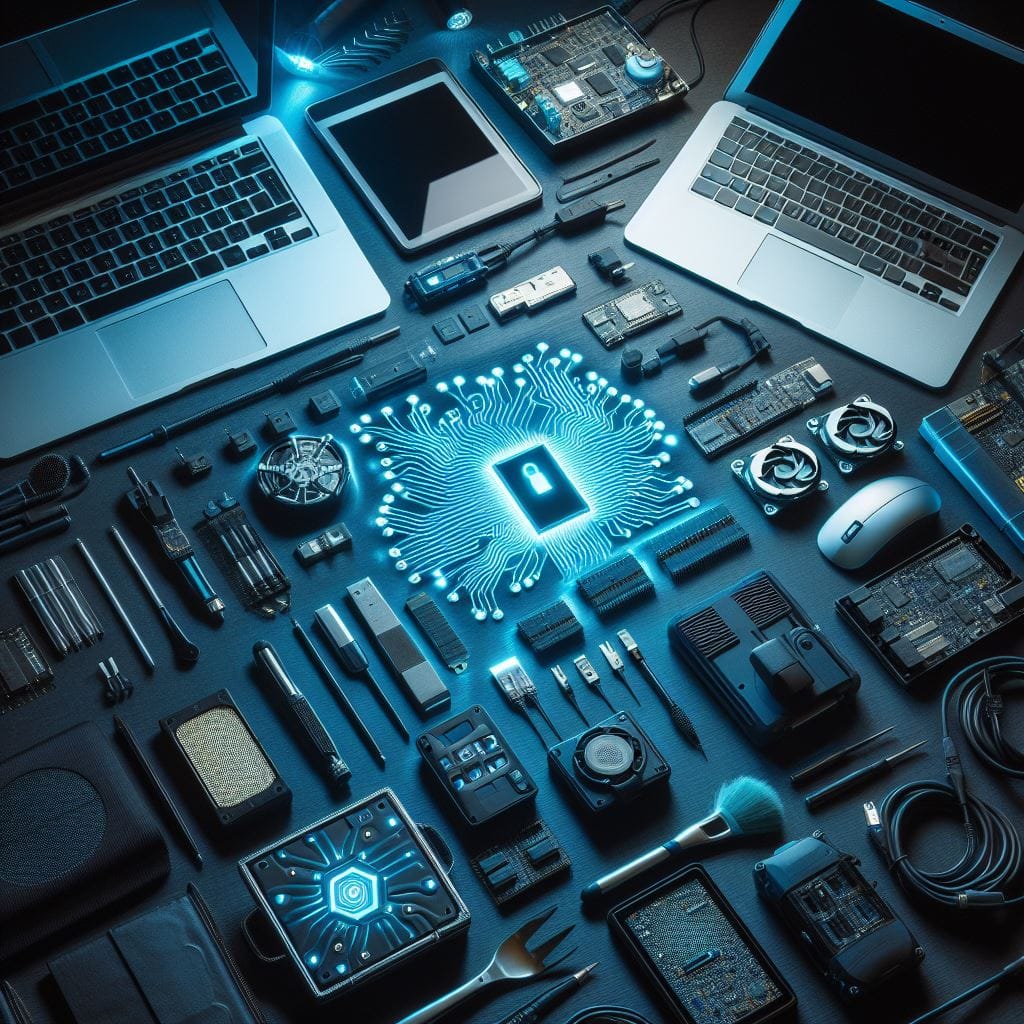
With member-exclusive content, I intend to offer material that reflects my unique perspective as a creator. This may include: - Configuration guides for specific tools. - Reflections on new tools and initial impressions. - Personal opinions on current cybersecurity events. - Other exclusive content deemed particularly noteworthy.
A collection of 12 posts:
12 min read
Members only
There's generally a tool for everything in cybersecurity - but I've made an attempts to list all the tools I come across in my work and studies.

3 min read
Members only
The space of cybersecurity is known for having a lot of terms and acronyms to keep track of. Here's a handy page with all the terminology I've come across!

3 min read
Members only
Even though Phishing is the most common of Social Engineering techniques - there are many others. Here are my notes I've taken!

64 min read
Members only
Offensive security is just as important as pure defensive action and just as fun! Here I have my long, long list of notes structured after Mitre Attack.

2 min read
Members only
Python is a very popular and powerful programming- and scripting language, which makes it all so powerful within cybersecurity. Here are my notes from my python experiences!

3 min read
Members only
PowerShell is crucial when exploring a Windows environment, both as an attack and a defender. Therefore I have this page related to Powershell.

8 min read
Members only
There are so many things one does not want to forget, thus this is my "Misc" note with small fixes and stuff that doesn't belong in any other category.

2 min read
Members only
In-data isn't always structured like you want it to be. To structure it yourself it is a common practise to use Regular expression (RegEx) together with tools such as sed, grep and awk. Here you will see how to use them!